WEBSITE
Optimizing Business Security with jabil.okta

In the rapidly evolving digital landscape, ensuring robust security measures is crucial for businesses to safeguard their sensitive data and protect their operations. The emergence of cloud-based applications and remote workforces has increased the demand for a reliable and efficient authentication system. Enter jabil.okta, a leading identity and access management solution that empowers organizations with seamless user authentication, strong security protocols, and simplified access management.k
What is jabil.okta?
jabil.okta is an industry-leading identity and access management platform that provides a unified, secure, and scalable solution for businesses to manage user identities and control access to their resources. This cloud-based platform enables organizations to enhance security, improve user experience, and streamline various aspects of identity management.
Why Choose jabil.okta?
- Unrivaled Security: jabil.okta offers robust security measures, including multi-factor authentication, adaptive access policies, and encryption, ensuring that only authorized individuals gain access to critical resources.
- Seamless Integration: With its extensive integration capabilities, jabil.okta can seamlessly connect with numerous applications and systems, providing a smooth and efficient user experience.
- Scalability: Whether you are a small business or a large enterprise, jabil.okta can effortlessly scale to meet your organization’s evolving needs.
- User-Friendly Interface: The platform’s intuitive user interface simplifies the onboarding process, reducing the burden on IT teams and enhancing user satisfaction.
The Key Features of jabil.okta
Single Sign-On (SSO) Functionality
jabil.okta’s SSO functionality allows users to access multiple applications and services with just one set of credentials. This eliminates the need for remembering multiple passwords, boosting productivity, and reducing password-related security risks.
Multi-Factor Authentication (MFA)
MFA adds an extra layer of security by requiring users to provide multiple forms of identification before gaining access. This can include something they know (password), something they have (smartphone), and something they are (fingerprint), significantly reducing the risk of unauthorized access.
Adaptive Access Policies
jabil.okta’s adaptive access policies use machine learning algorithms to assess user behavior and risk factors. Based on this evaluation, access policies are dynamically adjusted, providing additional security measures when necessary, without compromising user experience.
Lifecycle Management
The platform offers comprehensive identity lifecycle management, ensuring smooth user onboarding, role-based access control, and automated deprovisioning when employees leave the organization. This reduces administrative overhead and enhances security.
Universal Directory
jabil.okta’s Universal Directory serves as a centralized repository for user identities, enabling IT teams to manage user profiles efficiently and synchronize user data across various systems and applications.
API Access Management
The platform supports API access management, enabling organizations to secure APIs, control access, and monitor usage efficiently. This is particularly beneficial for businesses with extensive API integrations.
Single Source of Truth
jabil.okta serves as the authoritative source of truth for user identities, ensuring consistency and accuracy across all connected applications and systems.
Secure Mobility
With jabil.okta, businesses can securely manage mobile access, allowing employees to work from any device without compromising data security.
Leveraging jabil.okta for Business Success
Implementing jabil.okta can revolutionize your organization’s security landscape and elevate your business to new heights. By harnessing the power of this cutting-edge identity and access management platform, you can achieve the following:
Enhanced Security and Data Protection
jabil.okta’s advanced security features safeguard your organization against cyber threats, data breaches, and unauthorized access. With robust authentication protocols and adaptive access policies, you can rest assured that your sensitive information remains protected.
Increased Productivity and Efficiency
By eliminating the need for multiple passwords and simplifying the login process through SSO, jabil.okta streamlines user authentication, leading to increased productivity and reduced login-related frustrations.
Compliance and Audit Readiness
Meeting regulatory requirements is crucial for every business. jabil.okta assists in ensuring compliance with various industry standards and provides audit logs for tracking user access, helping your organization stay compliant.
Seamless User Experience
The platform’s user-friendly interface and smooth integration capabilities contribute to an exceptional user experience. Employees can access the tools and resources they need effortlessly, boosting overall satisfaction and productivity.
Cost Savings and Scalability
jabil.okta’s cloud-based nature eliminates the need for extensive infrastructure investments. Additionally, the platform can easily scale with your business as it grows, making it a cost-effective and future-proof solution.
FAQs (Frequently Asked Questions)
Is jabil.okta suitable for small businesses?
Absolutely! jabil.okta is designed to cater to businesses of all sizes. Its scalable nature allows small businesses to implement the platform without worrying about outgrowing it as they expand.
How does jabil.okta ensure data security?
jabil.okta employs various security measures, such as multi-factor authentication, adaptive access policies, and encryption, to protect data from unauthorized access and cyber threats.
Can jabil.okta integrate with existing applications?
Yes, jabil.okta boasts extensive integration capabilities, allowing seamless connections with a wide range of applications and systems.
Is jabisl.okta compliant with industry standards?
Yes, jabil.okta complies with industry standards and regulations, making it suitable for businesses operating in regulated environments.
How does jabils.okta simplify user onboarding?
jabil.okta’s lifecycle management features automate user onboarding, ensuring a smooth and efficient process for new employees.
Does jabils.okta offer mobile access management?
Yes, jabil.okta provides secure mobile access management, enabling employees to work from any device without compromising data security.
Conclusion
In the digital era, safeguarding your business’s sensitive data and ensuring secure access to resources is paramount. jabil.okta emerges as a reliable and powerful identity and access management solution, offering unparalleled security, seamless integration, and a user-friendly experience. By implementing jabil.okta, businesses can enhance security, streamline operations, and unlock a new level of productivity and efficiency.
WEBSITE
Been Verified Login: Information at Your Fingertips

Been Verified, is a useful tool that helps you find what you need quickly and easily by following the instructions. Been Verified Login and trustworthy information is essential in today’s fast-paced environment. A reliable internet service like Been Verified is invaluable whether you’re trying to track down a long-lost buddy, confirm someone’s identity, or just indulge your natural curiosity. This detailed tutorial will show you how to sign up for Been Verified and will explain the features and benefits of the service.
Searching for the ultimate Been Verified user manual? Learn about the many advantages and other resources available to you. Join Been Verified now to have access to a wealth of verified information.
What is Been Verified?
Been Verified is a website that provides several resources for people searching, background checks, and public records. An intuitive user interface makes it possible to quickly and easily access data about people, places, and things. Been Verified login compiles information from several sources into thorough reports that aid in decision making.
Why Should You Use Been Verified?
You should use Been Verified because…
- There are a number of benefits to using Been Verified loginthat make it a great option for anyone looking for trustworthy data:
- Been Verified provides access to a plethora of public documents, such as arrest records, court records, marriage and divorce records, and more.
- Been Verified makes it easy to access the data you need with its straight forward interface.
- Been Verified gathers information from a wide variety of sources to provide you with detailed reports that give you a complete picture of a person’s history.
- Been Verified provides peace of mind by providing accurate and up-to-date information, whether you’re using it to evaluate new workers, reconnect with long-lost acquaintances, or verify your own internet presence.
Signing Up for Been Verified Login Process
In order to use Been Verified login, you must first register . Here is a detailed tutorial on how to begin:
- Start by clicking on this link to access the Been Verified website directly:
- To begin your search, either click the “Sign Up” or “Start Searching” button.
- Third, pick a subscription tier that works for you.
- Give your name, address, and credit card information.
- Establish a BeenVerified login ID and password.
- Take a look at the disclaimer and privacy statement.
- To finish signing up, go to the signup page and click the “Create Account” or “Sign Up” button.
- After signing up, enter your selected login information to access your Been Verified account.
- Your Been Verified Login process is successful.
Navigating the Been Verified Dashboard
After you log in, you’ll see the Been Verified dashboard, which serves as a centre from which you can access the service’s many features. The interface is designed to be simple and straightforward so that you can go about with ease. Some of the most important parts of the dashboard are as follows:
- You may initiate a search by entering a name, phone number, email address, or other piece of information into the search bar.
- You may view a history of your search results under “Recent Reports.”
- In the Account Settings section, you may view and change your current subscription, as well as amend your billing and payment information.
- You may get answers to commonly asked issues, reach out to support, and sift through more materials in the “Help and Support” section.
Performing a Background Check
- Using Been Verified background check, you may learn important details about a person’s past. To do a background check, do the following:
- Simply type the individual’s name into the search field.
- Second, be as specific as possible on the location.
- Select the “Search” tab and click there.
- The fourth step is for Been Verified to search its massive database and produce a comprehensive report.
- Look into the various parts of the report, some of which may contain arrest records, addresses, phone numbers, email addresses, and social media accounts.
Unveiling Public Records with Been Verified
Been Verified, provides you with access to several public documents from which you may learn a great deal. Common categories of public documents include:
- Find out about any arrests, convictions, or sex offender registrations with the help of the FBI’s Criminal Records database.
- Legal proceedings, bankruptcies, and judgements are all documented in the public domain database known as “Court Records.”
- Find out if someone has been married or divorced, as well as the dates and places associated with such events, by searching marriage and divorce records.
- Access information about property ownership, addresses, and estimated values thanks to public property records.
- Bankruptcies, liens, and monetary judgements might all be uncovered by perusing the financial records available.
Finding People with Been Verified
Been Verified people search may help you track out anyone you’ve lost touch with, whether it’s an old pal or a long-lost family. Just do what I say:
- Simply type the individual’s name into the search field.
- Specify other information that will help narrow down the search, such as the person’s age or location.
- Select the “Search” tab and click there.
- Been Verified to search its database and produce a report with the results, which will include essential information including contact details and social media accounts.
- The Ins and Outs of Caller ID Lookup
Exploring Reverse Phone Lookup
If you have a phone number and want to find out more about it, you may use Been Verified reverse phone lookup service. Just do what I say:
- Start by doing a search for the number in question.
- Select the “Search” tab.
- when your query is processed, Been Verified will generate a report that may include the owner’s name, address, and other information from its database.
Discovering Email Information
Using only an email address and Been Verified, you can find out a lot of useful information. Just do what I say:
- Look up the address in the search field and click on it.
- Select the “Search” tab.
- Been Verified will then search its database and produce a report with details on the email address, including the owner’s identity, social media accounts, and more.
How to Use Been Verified for Social Media Searches
With Been Verified, you may look into someone’s social media profiles and learn more about their online life. Just do what I say:
- Simply type the individual’s name into the search field.
- Select the “Search” tab.
- Third, Been Verified will do a search across its database and produce a report with links to any social media accounts it finds matching the name.
Been Verified for Property Search
You may learn more about properties and their owners with the help of Been Verifier’s property search function. Use it as follows:
- Type the address into the search bar.
- Select the “Search” tab.
- Been Verified will then do a search of its database and generate a report for you that includes information such as the property’s history of ownership and more.
Receiving Alerts and Notifications
Been Verified provides a system of alerts and notifications to inform you of relevant developments. The process is as follows:
- First, create notifications that are triggered when certain search terms are met (e.g., a person’s name, phone number, or email address).
- If additional information meeting your criteria becomes available, Been Verified will let you know.
- Keep up with any and all changes to your criminal record, residence, and other pertinent information.
Utilizing the Mobile App
You may use the capabilities of Been Verified anywhere thanks to the app available for both iOS and Android smartphones. Some advantages of utilising the mobile app are as follows:
- Search and see reports whenever and wherever you choose.
- Get updates whenever there are important announcements or notices.
- Access previously searched reports and saved searches with ease thanks to the app’s well-designed layout
Conclusion
Been Verified, is a useful tool that helps you find what you need quickly and easily. Following the instructions below, you’ll be able to access Been Verified, peruse its features, and mine public data for insights. Always make sure you’re staying within the law when using this tool. The sooner you get started with Been Verified, the sooner you’ll have access to a variety of information.
Read more on : Been Verified Login
SOCIAL MEDIA
CoreComm Login: Managing Your Online Experience

In today’s fast-paced digital world, where communication and connectivity reign supreme, having a reliable and user-friendly online platform is crucial. This is where CoreComm comes into play with its efficient and streamlined login system. In this comprehensive guide, we’ll delve into the ins and outs of CoreComm Login, exploring its features, benefits, and how it empowers users to take control of their online experiences.
1. Introduction: Navigating the Digital Landscape with CoreComm Login
In the era of instant communication and online interactions, CoreComm Login emerges as a bridge between users and a multitude of digital services. This article serves as your compass to understand and utilize the features that this platform offers to enhance your online engagement.
2. Understanding CoreComm: A Brief Overview
CoreComm stands as a pioneering force in the realm of telecommunications, providing a comprehensive suite of communication services. From high-speed internet to digital voice solutions, CoreComm caters to both residential and business needs, aiming to simplify the way we connect in the digital age.
3. The Significance of CoreComm Login
Your CoreComm account is your gateway to a world of digital convenience. By logging in, you unlock the ability to manage your communication services, pay bills online, access support, and customize your preferences – all from one centralized platform.
4. Getting Started with CoreComm Login
Initiating your journey with CoreComm is a breeze. Simply visit the official website and locate the “Login” button. Enter your registered credentials, including your username and password, to access your account.
5. Key Features of CoreComm Login
CoreComm Login offers an array of user-centric features designed to simplify your online experience. These include:
- Service Management: Effortlessly manage your subscribed services, upgrade or modify plans, and explore new offerings to suit your evolving needs.
- Bill Payment: Say goodbye to traditional payment methods. With CoreComm Login, you can conveniently pay your bills online, view billing history, and set up auto-pay options for a hassle-free experience.
- 24/7 Support: Encountering issues or seeking assistance? CoreComm provides round-the-clock support through its online platform, ensuring your queries are addressed promptly.
6. Navigating Your Account Dashboard
Upon logging in, you’ll find yourself on the intuitive account dashboard. This hub serves as your command center, offering quick access to various features and tools.
7. Managing Your Communication Services
From managing your internet speed to tweaking your digital voice settings, CoreComm Login lets you take control of your communication services. Easily upgrade your plan, monitor usage, and explore additional features to enhance your connectivity.
8. Troubleshooting and Support
Even the smoothest digital experiences can hit a bump. But fear not – CoreComm Login provides comprehensive troubleshooting guides and direct support options to resolve issues swiftly. Access an extensive knowledge base to find solutions to common problems, or initiate a support ticket for personalized assistance.
9. Security Measures: Protecting Your CoreComm Account
Safeguarding your online presence is paramount. CoreComm Login implements robust security measures to ensure your personal information remains confidential. Utilize two-factor authentication, update your password regularly, and stay informed about the latest security practices to fortify your account.
10. Embracing the Future of Connectivity with CoreComm
As technology continues to evolve, CoreComm remains committed to delivering innovative solutions that redefine connectivity. By embracing CoreComm Login, you’re not only accessing current services but also securing a portal to the future of communication.
Conclusion
In the grand tapestry of digital existence, CoreComm Login stands as a key thread that weaves convenience, control, and connectivity together. As you embark on your journey with this platform, remember that every click, setting adjustment, and interaction is a step toward unlocking the full potential of your online experience. Seamlessly managing your communication services has never been this empowering – thank you for choosing CoreComm Login.
WEBSITE
U-Haul Life Login: Employee Resources and Benefits
In today’s digital age, staying connected and accessing important resources has never been easier. U-Haul, a renowned leader in the moving and storage industry, understands the significance of providing its employees with seamless access to vital information. This article delves into the U-Haul Life login portal, demonstrating how it empowers employees to manage their professional journey effectively while highlighting the key benefits and features it offers.
1. Introduction
As an employee at U-Haul, you’re part of a dynamic team committed to providing top-notch moving and storage solutions. U-Haul recognizes the value of an empowered workforce and offers the U-Haul Life login platform, designed to make your professional journey smoother.
2. Understanding U-Haul Life Login
The U-Haul Life login portal serves as a central hub for all your employment-related needs. Accessible 24/7 from any device with an internet connection, this portal ensures that you can conveniently manage various aspects of your professional life.
3. Features of U-Haul Life Login Portal
– Accessing Payroll Information
No more waiting for paper pay stubs! With U-Haul Life, you can effortlessly access your payroll information online. Whether you need to view past pay statements or check your current earnings, this feature puts the information at your fingertips.
– Exploring Training and Development Resources
Continuous learning is a cornerstone of personal and professional growth. U-Haul Life offers a plethora of training and development resources that empower you to enhance your skills, ensuring you’re always prepared to take on new challenges.
– Managing Employee Benefits
U-Haul is committed to the well-being of its employees. Through the U-Haul Life portal, you can manage your benefits, review health insurance options, and make informed decisions about your coverage.
– Staying Updated with Company News
Stay informed about company updates, events, and announcements through the U-Haul Life portal. Whether it’s a new branch opening or a recognition program, you won’t miss a beat.
– Employee Assistance Programs
U-Haul recognizes that life can sometimes present challenges. The portal provides access to employee assistance programs that offer support and resources for various life situations.
4. Accessing Payroll Information
To access your payroll information, simply log in to the U-Haul Life portal using your unique credentials. Once logged in, navigate to the “Payroll” section, where you can view and download your pay stubs, track your earnings, and access tax-related documents.
5. Exploring Training and Development Resources
Continuous learning is a key aspect of personal and professional growth. U-Haul Life’s “Training and Development” section offers a wide range of online courses, webinars, and resources to help you enhance your skills and stay ahead in your career.
6. Managing Employee Benefits
Your well-being matters to U-Haul. Within the U-Haul Life portal, you can review and manage your employee benefits. From health insurance to retirement plans, everything is accessible with just a few clicks.
7. Staying Updated with Company News
The “Company News” section of the U-Haul Life portal keeps you in the loop about the latest happenings. Whether it’s a product launch, a community initiative, or an employee recognition story, you’ll find it all here.
8. Employee Assistance Programs
Life can present challenges both inside and outside of work. U-Haul Life provides access to employee assistance programs that offer resources, guidance, and support for a wide range of personal and professional issues.
9. U-Haul for a Sustainable Future
U-Haul is not just a moving and storage company; it’s committed to sustainability. The U-Haul Life portal showcases the company’s efforts towards a greener future, from eco-friendly initiatives to community involvement.
10. FAQs About U-Haul Life Login
Q1: How do I access the U-Haul Life login portal? A: You can access the portal by visiting www.uhaullife.com and entering your login credentials.
Q2: Can I access the portal from my mobile device? A: Absolutely! The U-Haul Life portal is designed to be responsive and accessible from any device with internet connectivity.
Q3: Are the training resources tailored to specific roles? A: Yes, the training resources cover a wide range of roles and departments, ensuring that everyone can find relevant and valuable learning opportunities.
11. Conclusion
The U-Haul Life login portal serves as a powerful tool that enables employees to manage their professional journey with ease. From payroll information to training resources and employee benefits, U-Haul Life empowers you to take control of your career. Stay connected, informed, and prepared for the future with U-Haul Life.
-

 Marketing1 year ago
Marketing1 year agoHow Often Should You Publish on a Blog?
-
 Technology1 year ago
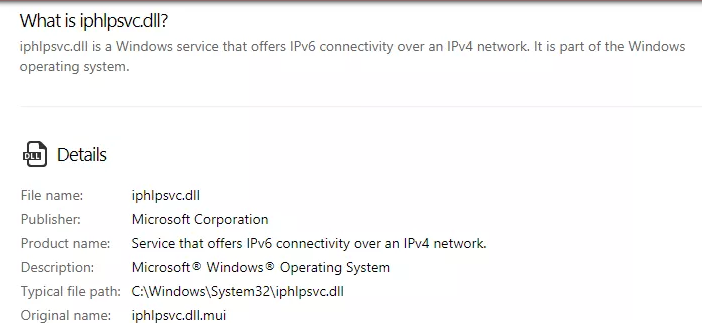
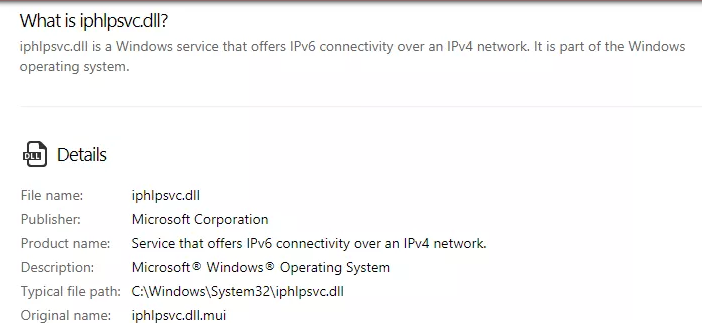
Technology1 year agoIPHLPSVC Services Tuning? Windows 7/10
-
 Technology1 year ago
Technology1 year agoHow AI Can Transform Healthcare
-

 REVIEWS1 year ago
REVIEWS1 year agoBest Gaming Communities Like F95zone
-

 OUTDOOR1 year ago
OUTDOOR1 year agoColoring Black and White Photo at Home
-
 Technology1 year ago
Technology1 year ago5 Best React JS UI Frameworks for Swift Prototyping
-

 REVIEWS1 year ago
REVIEWS1 year agoAll You Need to Know About KissAnime – Is it Safe and Legal?
-

 GAMING1 year ago
GAMING1 year agoPick N Mix: A Slots Adventure for Everyone
